CVE-2021-26855
CVE-2021-26855 ssrf 简单利用 golang 练习
影响版本
Exchange Server 2013 小于 CU23 Exchange Server 2016 小于 CU18 Exchange Server 2019 小于 CU7
利用条件
该漏洞不同于以往的 exchange 漏洞,此漏洞并不需要一个可登录的用户身份,可以在未授权的情况下获取内部用户资源,配合 CVE-2021-27065 可以实现远程命令执行。
漏洞触发必要条件
- 目标服务器存在漏洞
- 目标 exchange 服务器必须为负载均衡服务器,即同时使用两台及以上服务器
- 目标邮箱地址,注意,该地址需要为域内邮件地址而非邮箱地址,二者存在差异
- 攻击者还必须标识内部Exchange服务器的完全限定域名(FQDN)
以上四项中,FQDN 可以通过 ntlm type2 消息抓取;邮件地址可以直接枚举。
使用说明
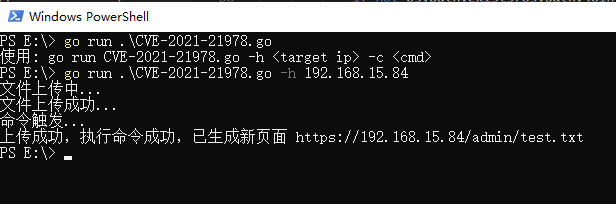
这一漏洞利用,使用脚本语言如 ruby python 等更为方便,用 golang 写主要是学习 golang,因此这个小工具只能算半成品,有时间再更新。
本工具支持漏洞检测,用户枚举,可以实现简单的邮件 id、标题读取(其实就是xml内容修改) 后续利用可以参考8581,都是提交 xml。
用法:
go run CVE-2021-21978.go -h <target ip>
-h string 必填,目标地址或域名
-U string 选填,需要枚举的用户列表
-d 选填,下载邮件
-l 选填,列出邮件列表
-n string 选填,需要指定 FQND 事填写
-t string 选填,请求延迟时间 (default "1")
-u string 选填,指定目标 (default "administrator")
更新下载功能



![Confluence OGNL Injection [CVE-2021-26084].](https://user-images.githubusercontent.com/44043159/132096348-db727da8-bf00-457a-a09d-26599743b145.jpg)