sakuraji_log4j
This tool is used to discover and remedidate the Log4Shell vulnerability [CVE-2021-45105] by removing the 'JndiLookup.class' file from '.ear|.jar|.war' files on Windows, Linux & Mac OS.
Usage:
Scan OS for Log4Shell vulnerability.
- sakuraji_log4j discover
- Example: https://i.imgur.com/VgXCrH1.png
Scan OS and remediate Log4Shell vulnerability.
- sakuraji_log4j remediate
- Example: https://i.imgur.com/JijGWj7.png
Build:
Clone & go build .
Discover and remediate Log4Shell vulnerability [CVE-2021-45105]
Owner
Sakuraji
Similar Resources
Log4j 2 (CVE-2021-44228) vulnerability scanner for Windows OS
log4j-scanner Log4j 2 (CVE-2021-44228) vulnerability scanner for Windows OS. Example Usage Usage .\log4j-scanner.exe Terminal is used to output resul
Tool to check whether one of your applications is affected by a vulnerability in log4j: CVE-2021-44228
log4shell.tools log4shell.tools is a tool allows you to run a test to check whether one of your applications is affected by a vulnerability in log4j:
Scans and catches callbacks of systems that are impacted by Log4J Log4Shell vulnerability across specific headers.
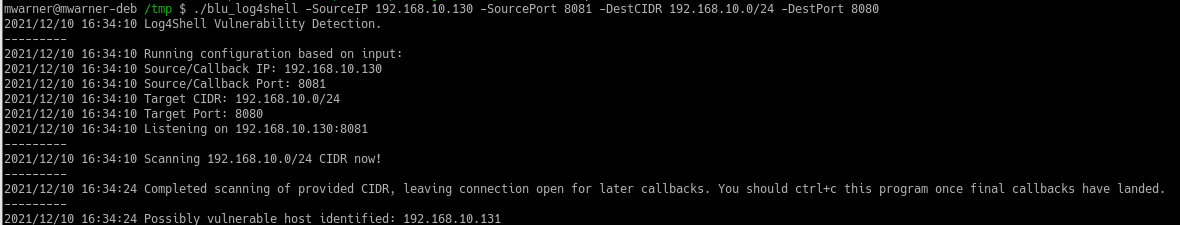
Log4ShellScanner Scans and catches callbacks of systems that are impacted by Log4J Log4Shell vulnerability across specific headers. Very Beta Warning!
A tool for checking log4shell vulnerability mitigations
log4shell-ldap A tool for checking log4shell vulnerability mitigations. Usage: Build a container image: docker build . -t log4shell Run it: docker run
CVE-2021-21978 exp
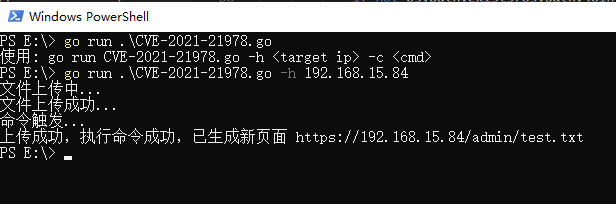
CVE-2021-21978 CVE-2021-21978 RCE exp 影响版本 VMware View Planner Harness 4.X 与 CVE-2021-21978 类似,该漏洞可以在未授权访问的情况下,上传任意文件,并通过修改自带 py 脚本实现远程代码执行。
CVE-2021-26855 exp

CVE-2021-26855 CVE-2021-26855 ssrf 简单利用 golang 练习 影响版本 Exchange Server 2013 小于 CU23 Exchange Server 2016 小于 CU18 Exchange Server 2019 小于 CU7 利用条件 该漏洞不
CVE-2021-26855 exp
CVE-2021-26855 CVE-2021-26855 ssrf 简单利用 golang 练习 影响版本 Exchange Server 2013 小于 CU23 Exchange Server 2016 小于 CU18 Exchange Server 2019 小于 CU7 利用条件 该漏洞不
Exploit for HiveNightmare - CVE-2021–36934
HiveNightmare this is a quick and dirty exploit for HiveNightmare (or SeriousSam) - CVE-2021–36934 This allows non administrator users to read the SAM
CVE-2021-3449 OpenSSL denial-of-service exploit 👨🏻💻
CVE-2021-3449 OpenSSL 1.1.1k DoS exploit Usage: go run . -host hostname:port This program implements a proof-of-concept exploit of CVE-2021-3449 affe
Related tags
Scanner to send specially crafted requests and catch callbacks of systems that are impacted by Log4J Log4Shell vulnerability (CVE-2021-44228)
scan4log4shell Scanner to send specially crafted requests and catch callbacks of systems that are impacted by Log4J Log4Shell vulnerability CVE-2021-4
Detect and fix log4j log4shell vulnerability (CVE-2021-44228)
log4fix This tool is to detect and fix the log4j log4shell vulnerability (CVE-2021-44228) by looking and removing the JndiLookup class from .jar/.war/
A FreeSWITCH specific scanning and exploitation toolkit for CVE-2021-37624 and CVE-2021-41157.
PewSWITCH A FreeSWITCH specific scanning and exploitation toolkit for CVE-2021-37624 and CVE-2021-41157. Related blog: https://0xinfection.github.io/p
Poc-cve-2021-4034 - PoC for CVE-2021-4034 dubbed pwnkit
poc-cve-2021-4034 PoC for CVE-2021-4034 dubbed pwnkit Compile exploit.go go buil
CVE-2021-4034 - A Golang implementation of clubby789's implementation of CVE-2021-4034
CVE-2021-4034 January 25, 2022 | An00bRektn This is a golang implementation of C
Scans files for .jars potentially vulnerable to Log4Shell (CVE-2021-44228) by inspecting the class paths inside the .jar.
log4shelldetect Scans a file or folder recursively for jar files that may be vulnerable to Log4Shell (CVE-2021-44228) by inspecting the class paths in
A Smart Log4Shell/Log4j/CVE-2021-44228 Scanner
Log4Shell Sentinel - A Smart CVE-2021-44228 Scanner Introduction While there have some excellent tools released to help organizations scan their envir
A fast tool to mass scan for a vulnerability on Microsoft Exchange Server that allows an attacker bypassing the authentication and impersonating as the admin (CVE-2021-26855).
proxylogscan This tool to mass scan for a vulnerability on Microsoft Exchange Server that allows an attacker bypassing the authentication and imperson
Proof-of-Concept tool for CVE-2021-29156, an LDAP injection vulnerability in ForgeRock OpenAM v13.0.0.
CVE-2021-29156 Proof-of-Concept (c) 2021 GuidePoint Security Charlton Trezevant [email protected] Background Today GuidePoint
A minimalistic LDAP server that is meant for test vulnerability to JNDI+LDAP injection attacks in Java, especially CVE-2021-44228.
jndi-ldap-test-server This is a minimalistic LDAP server that is meant for test vulnerability to JNDI+LDAP injection attacks in Java, especially CVE-2