51 Resources
Golang cve Libraries
Simple webhook to block exploitation of CVE-2022-0811
webhook-cve-2022-0811 This is a really simple webhook that just blocks pod creation if malicious sysctl values are configured. Build go test CGO_ENABL
Vulnerability scanner for Spring4Shell (CVE-2022-22965)
go-scan-spring Vulnerability scanner to find Spring4Shell (CVE-2022-22965) vulnerabilities For more information: https://www.fracturelabs.com/posts/ef
A golang based exp for CVE-2021-4034 dubbed pwnkit (more features added......)

PwnKit-go-LPE (CVE-2021-4034) A golang based exp for CVE-2021-4034 dubbed pwnkit @@@@@@@ @@@ @@@ @@@ @@@ @@@ @@@ @@@ @@@ @@@@@@@
A pure-Go implementation of the CVE-2021-4034 PwnKit exploit
go-PwnKit A pure-Go implementation of the CVE-2021-4034 PwnKit exploit. Installation git clone [email protected]:OXDBXKXO/go-PwnKit.git cd go-PwnKit make
Pwnkit-go - Exploit for the PwnKit vulnerability, CVE-2021-4034, written in Go
Pwnkit-go This is a working exploit for the pwnkit vulnerability, CVE-2021-4034,
CVE-2021-4034 - A Golang implementation of clubby789's implementation of CVE-2021-4034
CVE-2021-4034 January 25, 2022 | An00bRektn This is a golang implementation of C
Poc-cve-2021-4034 - PoC for CVE-2021-4034 dubbed pwnkit
poc-cve-2021-4034 PoC for CVE-2021-4034 dubbed pwnkit Compile exploit.go go buil
Finds an identifiable hash value for each version of GitLab vulnerable to CVE-2021-22205
Finds an identifiable hash value for each version of GitLab vulnerable to CVE-2021-22205
Discover and remediate Log4Shell vulnerability [CVE-2021-45105]
sakuraji_log4j This tool is used to discover and remedidate the Log4Shell vulnerability [CVE-2021-45105] by removing the 'JndiLookup.class' file from
A Smart Log4Shell/Log4j/CVE-2021-44228 Scanner
Log4Shell Sentinel - A Smart CVE-2021-44228 Scanner Introduction While there have some excellent tools released to help organizations scan their envir
Detect and fix log4j log4shell vulnerability (CVE-2021-44228)
log4fix This tool is to detect and fix the log4j log4shell vulnerability (CVE-2021-44228) by looking and removing the JndiLookup class from .jar/.war/
A Log4J Version 2 Detector written in golang
Installation From source: go install github.com/juergenhoetzel/log4j2go/cmd/log4
Look for JAR files that vulnerable to Log4j RCE (CVE‐2021‐44228)

Look4jar Look for JAR files that vulnerable to Log4j RCE (CVE‐2021‐44228) Objectives It differs from some other tools that scan for vulnerable remote
Check and exploit log4j2 vulnerability with single Go program.

Log4Shell Check and exploit log4j2 vulnerability with single Go program. You don't need to install anything except develop it. It supports ldaps and h
Tools for remediating the recent log4j2 RCE vulnerability (CVE-2021-44228)
log4j-remediation-tools Tools for finding and reproducing the CVE-2021-44228 log4j2 vulnerability Tools find-vulnerabilities: determine heuristically
Minecraft Honeypot for Log4j exploit. CVE-2021-44228 Log4Shell LogJam
Minecraft Log4j Honeypot This honeypots runs fake Minecraft server (1.7.2 - 1.16.5 without snapshots) waiting to be exploited. Payload classes are sav
A fully automated, reliable, super-fast, mass scanning and validation toolkit for the Log4J RCE CVE-2021-44228 vulnerability.

LogMePwn A fully automated, reliable, super-fast, mass scanning and validation toolkit for the Log4J RCE CVE-2021-44228 vulnerability. With enough amo
Tool to check whether one of your applications is affected by a vulnerability in log4j: CVE-2021-44228
log4shell.tools log4shell.tools is a tool allows you to run a test to check whether one of your applications is affected by a vulnerability in log4j:
Scanner to send specially crafted requests and catch callbacks of systems that are impacted by Log4J Log4Shell vulnerability (CVE-2021-44228)
scan4log4shell Scanner to send specially crafted requests and catch callbacks of systems that are impacted by Log4J Log4Shell vulnerability CVE-2021-4
Log4j 2 (CVE-2021-44228) vulnerability scanner for Windows OS
log4j-scanner Log4j 2 (CVE-2021-44228) vulnerability scanner for Windows OS. Example Usage Usage .\log4j-scanner.exe Terminal is used to output resul
Dockerized Go app for testing the CVE-2021-44228 vulnerability
docker-log4shell Simple Go app / Docker image for playing with the CVE-2021-44228 vulnerability. Hosts a simple file server and an ldap server that pr
Simple local scanner for vulnerable log4j instances
Simple local log4j vulnerability scanner (Written in Go because, you know, "write once, run anywhere.") This is a simple tool that can be used to find
A minimalistic LDAP server that is meant for test vulnerability to JNDI+LDAP injection attacks in Java, especially CVE-2021-44228.
jndi-ldap-test-server This is a minimalistic LDAP server that is meant for test vulnerability to JNDI+LDAP injection attacks in Java, especially CVE-2
Scans files for .jars potentially vulnerable to Log4Shell (CVE-2021-44228) by inspecting the class paths inside the .jar.
log4shelldetect Scans a file or folder recursively for jar files that may be vulnerable to Log4Shell (CVE-2021-44228) by inspecting the class paths in
PoC for CVE-2021-41277
CVE-2021-41277 PoC Metabase is an open source data analytics platform. Local File Inclusion issue has been discovered in some versions of metabase. He
A small server for verifing if a given java program is succeptibel to CVE-2021-44228
CVE-2021-44228-Test-Server A small server for verifing if a given java program is succeptibel to CVE-2021-44228 Usage Build the program using go build
Grafana Unauthorized arbitrary file reading vulnerability

CVE-2021-43798 Grafana Unauthorized arbitrary file reading vulnerability 8.3.1 (2021-12-07) Security: Fixes CVE-2021-43798 . For more information, see
Grafana Arbitrary File Reading Vulnerability
GrafanaArbitraryFileRead Usage 1. show info ❯ go run main.go -s [INF] VulnInfo: { "Name": "Grafana Ar
CVE-2021-43798 - Grafana 8.x Path Traversal (Pre-Auth)
CVE-2021-43798 Grafana 8.x Path Traversal (Pre-Auth) All credits go to j0v and his tweet https://twitter.com/j0v0x0/status/1466845212626542607 Disclai
A FreeSWITCH specific scanning and exploitation toolkit for CVE-2021-37624 and CVE-2021-41157.
PewSWITCH A FreeSWITCH specific scanning and exploitation toolkit for CVE-2021-37624 and CVE-2021-41157. Related blog: https://0xinfection.github.io/p
CVE 2021 41277
CVE-2021-41277 Usage 1. show help info ~/CVE-2021-41277 ❯ go run main.go -h Usage of main: -f string File containing li
CVE-2021-22205 RCE
CVE-2021-22205 CVE-2021-22205 RCE 工具仅用于分享交流,切勿用于非授权测试,否则与作者无关 -R string VPS to load tools eg: -R 127.0.0.1:8083 -T string Tool nam
A CVE-2021-22205 Gitlab RCE POC written in Golang
Golang-CVE-2021-22205-POC A bare bones CVE-2021-22205 Gitlab RCE POC written in Golang which affects Gitlab CE/EE 13.10.3 Gitlab CE/EE 13.9.6 Gitl
PoC for CVE-2015-1635 / MS15-034 - HTTP.sys Allows Remote Code Execution / Check & DOS

CVE-2015-1635 PoC for CVE-2015-1635 / MS15-034 - HTTP.sys Allows Remote Code Execution / Check & DOS ./MS15-034 URL RESOURCE FLAG [0 or 18] Note
Proof-of-Concept tool for CVE-2021-29156, an LDAP injection vulnerability in ForgeRock OpenAM v13.0.0.
CVE-2021-29156 Proof-of-Concept (c) 2021 GuidePoint Security Charlton Trezevant [email protected] Background Today GuidePoint
Unofficial but convenient Go wrapper around the NVD API
NVD API The NVD API is an unofficial Go wrapper around the NVD API. Supports: CVE CPE How to use The following shows how to basically use the wrapper
The NVD API is an unofficial Go wrapper around the NVD API.
NVD API The NVD API is an unofficial Go wrapper around the NVD API. Supports: CVE CPE How to use The following shows how to basically use the wrapper
Exploit for remote command execution in Golang go get command.
CVE-2018-6574 Exploit for remote command execution in Golang go get command. Introduction When you go get a package, Go is designed to build and insta
Exploitation of CVE-2018-18925 a Remote Code Execution against the Git self hosted tool: Gogs.

CVE-2018-18925 Exploitation of CVE-2018-18925 a Remote Code Execution against the Git self hosted tool: Gogs. Gogs is based on the Macaron framework.
CVE-2021-26084 - Confluence Server Webwork OGNL injection (Pre-Auth RCE)
CVE-2021-26084 Proof of concept for CVE-2021-26084. Confluence Server Webwork OGNL injection (Pre-Auth RCE) Disclaimer This is for educational purpose
Confluence OGNL Injection [CVE-2021-26084].
![Confluence OGNL Injection [CVE-2021-26084].](https://user-images.githubusercontent.com/44043159/132096348-db727da8-bf00-457a-a09d-26599743b145.jpg)
CVE-2021-26084 this is a script written in golang to exploit Confluence OGNL Injection [CVE-2021-26084]. git clone https://github.com/march0s1as/CVE-
CVE-2021-3449 OpenSSL denial-of-service exploit 👨🏻💻
CVE-2021-3449 OpenSSL 1.1.1k DoS exploit Usage: go run . -host hostname:port This program implements a proof-of-concept exploit of CVE-2021-3449 affe
Exploit for HiveNightmare - CVE-2021–36934
HiveNightmare this is a quick and dirty exploit for HiveNightmare (or SeriousSam) - CVE-2021–36934 This allows non administrator users to read the SAM
全新的开源漏洞测试框架,实现poc在线编辑、运行、批量测试。使用文档:

pocassist是一个 Golang 编写的全新开源漏洞测试框架。 简单易用 只需要在前端编辑,即可生成poc对批量目标进行测试 单二进制文件,无依赖,也无需安装 性能优秀 支持高并发,通过使用 ants实例化协程池,复用 goroutine 多重内存复用,尽可能小的内存占用 规则体系 完全兼容x
CVE-2021-26855 exp
CVE-2021-26855 CVE-2021-26855 ssrf 简单利用 golang 练习 影响版本 Exchange Server 2013 小于 CU23 Exchange Server 2016 小于 CU18 Exchange Server 2019 小于 CU7 利用条件 该漏洞不
vRealize RCE + Privesc (CVE-2021-21975, CVE-2021-21983, CVE-0DAY-?????)
REALITY_SMASHER vRealize RCE + Privesc (CVE-2021-21975, CVE-2021-21983, CVE-0DAY-?????) "As easy to stop as it is to comprehend." What is it? "Reality
Nuclei is a fast tool for configurable targeted vulnerability scanning based on templates offering massive extensibility and ease of use.

Fast and customisable vulnerability scanner based on simple YAML based DSL. How • Install • For Security Engineers • For Developers • Documentation •
CVE-2021-26855 exp

CVE-2021-26855 CVE-2021-26855 ssrf 简单利用 golang 练习 影响版本 Exchange Server 2013 小于 CU23 Exchange Server 2016 小于 CU18 Exchange Server 2019 小于 CU7 利用条件 该漏洞不
CVE-2021-21978 exp
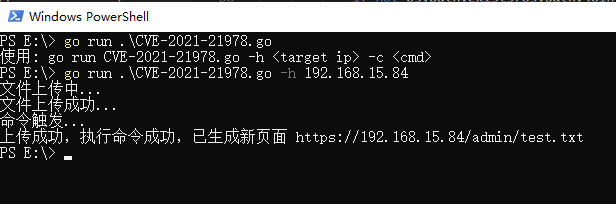
CVE-2021-21978 CVE-2021-21978 RCE exp 影响版本 VMware View Planner Harness 4.X 与 CVE-2021-21978 类似,该漏洞可以在未授权访问的情况下,上传任意文件,并通过修改自带 py 脚本实现远程代码执行。
A fast tool to mass scan for a vulnerability on Microsoft Exchange Server that allows an attacker bypassing the authentication and impersonating as the admin (CVE-2021-26855).
proxylogscan This tool to mass scan for a vulnerability on Microsoft Exchange Server that allows an attacker bypassing the authentication and imperson
Wprecon, is a vulnerability recognition tool in CMS Wordpress, 100% developed in Go.

WPrecon (Wordpress Recon) Hello! Welcome. Wprecon (Wordpress Recon), is a vulnerability recognition tool in CMS Wordpress, 100% developed in Go. Featu